Pro-leave Brexit Twitter activity boosted by suspicious activity, foreign support
Twitter’s efforts to rein in fake news and disinformation on the site have continued in 2019, but “suspicious activity” remains evident, according to a new research on Brexit Twitter activity on the site conducted by F-Secure. While unusual site activity was observed in favor of both leave and remain, it was far more prominent among the pro-leave group.
“Given the degree of suspicious activity observed, the researchers conclude that the pro-leave Twitter community is receiving support from far-right Twitter accounts based outside of the UK,” the report concludes.
Why Twitter matters as Brexit negotiations close
While Twitter is only the 12th most popular social network in the world, it remains a key platform for anyone seeking to influence political conversations.
Journalists rely on the site to gather leads and promote their work so much that academics have begun to study Twitter’s influence on shaping the news. Most of the world’s leaders are on the site, including the current president of the United States who finds it to be his favorite method of direct communication. It’s also the second most popular social media source for news in the United States
When it comes to the debate over Brexit, Twitter and other social media platforms have a direct line to 10 Downing Street—the work/live space of Theresa May, the current Prime Minister of the United Kingdom who is leading to negotiations to carry out the UK’s vote to leave the European Union conducted in 2016.
A “rapid response unit” of May’s government “is tasked with monitoring and firefighting stories set alight on social media, often beyond the radar of many of London’s politicians and journalists,” Politico reported.
Twitter is an ideal platform to observe how disinformation spreads
Suspicious Twitter activity is designed to imitate legitimate use of the site to avoid detection. Often, it is very effective.
“Architects of sophisticated social engineering campaigns, or astroturfing campaigns (fabricated social network interactions designed to deceive the observer into believing that the activity is part of a grass-roots campaign), sometimes create and operate convincing looking personas to assist in the propagation of content and messages relevant to their cause,” the report notes. “It is extremely difficult to distinguish these ‘fake’ personas from real accounts.”
Users seeking to game social networks can easily find ways to buy followers on the site or game the platform’s algorithms in various ways. More advanced operators can automate their efforts creating environment where content and data are produced much more quickly than it can be analyzed.
The report notes that Twitter provides “an ideal platform for research into social media attacks” thanks to its “open nature and fully-featured API support.”
Focusing on Brexit-centric Twitter activity
Researchers at F-Secure’s Artificial Intelligence Center of Excellence have been tracking misuse of the Twitter platform over the last two years, especially related to elections.
While the Brexit vote is long over, they decided to focus mentions of the term Brexit “in order to search for suspicious activity, disinformation campaigns, sentiment amplification, or other ‘meddling’ operations.”
Using the standard Twitter API and the python programming language, they tracked this activity between December 4th 2018 and January 27th 2019. The goal was to analyze to gage how often users were tweeting or sharing tweets on subject along with the influence of individual tweets, measured in retweets. They also monitored word counts, hashtags an urls used in the related tweets.
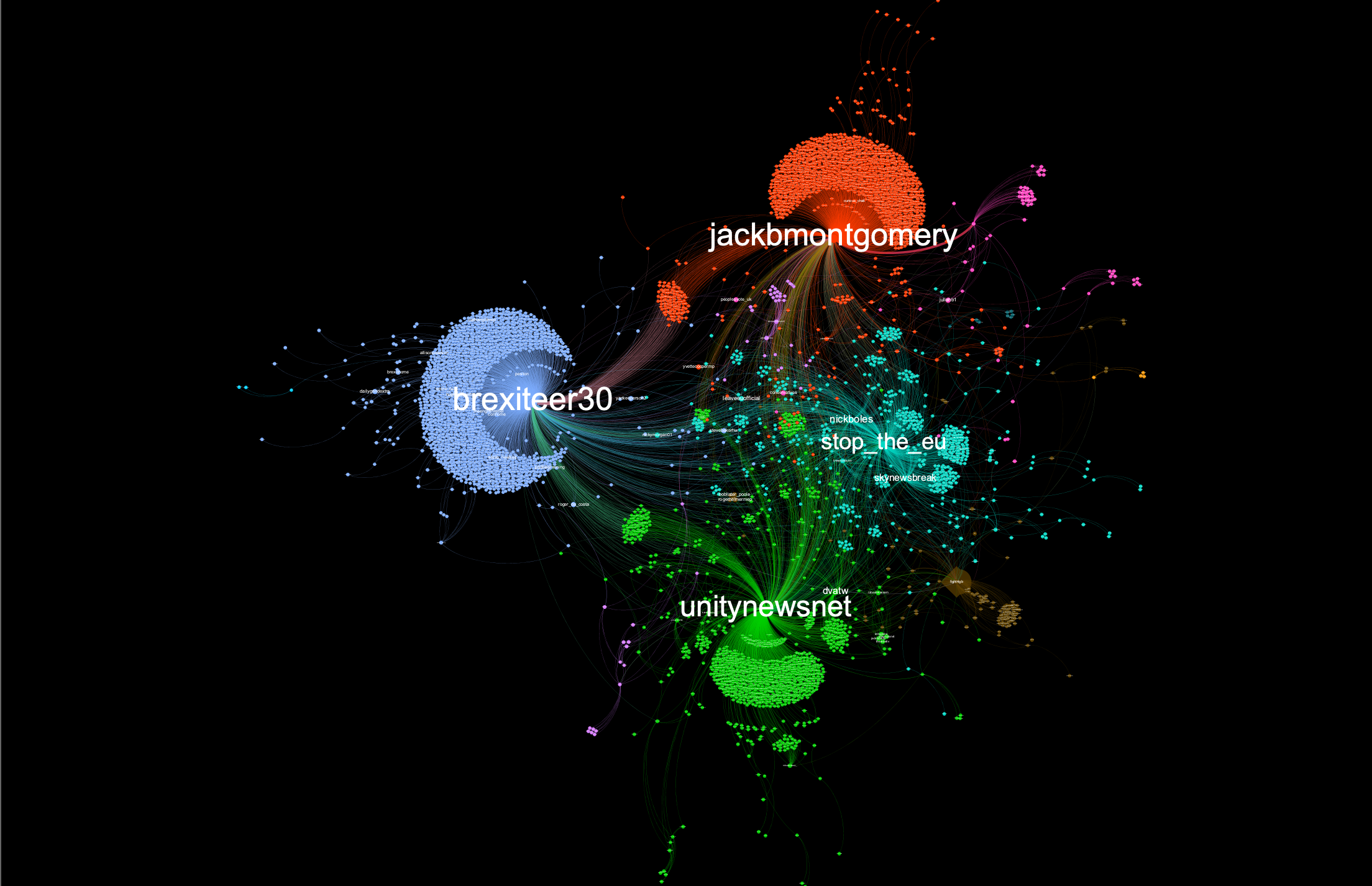
The visualization tool Gephi maps interactions between users:

Here’s what the first day of activity looked like, with the usernames of accounts most often pictured in a larger font:

What do the #franceprotest have to do with Brexit?
On December 11th, the researchers noticed an interesting phenomenon: the #franceprotests hashtag was flaring up inside the Brexit data.
The researchers mapped the interactions largely based on the popularity of just one tweet and got this:

Looking at the accounts active in this cluster, they found a number of them actively shared tweets related to the yellow vest movement (#yellowvest, #yellowjackets, #giletsjaunes), and to US right-wing topics (#MAGA, #qanon, #wwg1wga).
This suggested support for the hashtag was coming outside of France and from both sides of the Atlantic.
In addition, the researchers identified some suspicious accounts tweeting about the France protests and Brexit that seemed to be apolitical in nature. Only Twitter has the access to definitively determine whether these accounts have been co-opted for this amplification effort.
Pro-leave amplification flares
On the 20th of December, the researchers noticed a few accounts that had not been highly retweeted before breaking into his “top 50” of most influential—in terms of retweets and likes—accounts focused on Brexit.
Just a few tweets from pro-leave accounts brexiteer30, jackbmontgomery, unitynewsnet and stop_the_eu seemed to be at the center of this sudden flare up of anti-EU activity primarily coming from about 5,800 accounts.
This event also included support from accounts popular among the U.S. right wing, including Education4Libs and AmyMek, accounts with hundreds of thousands of followers.
December 20th happened to be the day that the first member of May’s cabinet—Work and Pensions Secretary Amber Rudd—suggested that a second “Leave” vote could occur, but the researchers did not find any data that connected this amplification to that event.
How to find suspicious activity on Twitter
Twitter’s user agreement bans “misuse [of] our Services.” But this misuse is rarely as obvious as a Twitter botnet, like the 22,000-strong one detected last year.
Continued research has the team a bit awed by how many potential insights may be available.
“There’s data hidden inside data – and there are many angles you can view it from, all of which highlight different phenomena,” a recent post on the importance of this work noted. “Social network data is like a living organism that changes from moment to moment.”
Graph analysis offers a “representation” of Twitter’s massive constant flow of content that allows some visibility into use of the site that veers toward “scams, social engineering, disinformation, sentiment amplification, and astroturfing campaigns.”
What’s so suspicious about the pro-leave activity
While some of the suspicious activity was found in both sides of the Brexit debate, the pro-leave efforts were more prominent and likely more effective in influencing the online conversation.
The report lists examples of suspicious behavior found to be supporting the pro-leave effort:
- The top two influencers in the pro-leave community received a disproportionate number of retweets, as compared to influencer patterns seen in the pro-remain community
- The pro-leave group relied on support from a handful of non-authoritative news sources
- A significant number of non-UK accounts were involved in pro-leave conversations and retweet activity
What’s next?
“It is very difficult to determine whether a Twitter account is a bot, or acting as part of a coordinated astroturfing campaign simply by performing queries with the standard API,” the research concludes in the “Final thoughts” section of the report.
The dataset includes “approximately 24 million tweets published by over 1.65 million users”—an amount of data that’s impossible for a small team of researchers to properly analyze, regardless of how inveterate they are.
Given how crucial the site is to debates and elections that may be settled by just a few percentage points or the interpretations of a rapid response team weighing a dashboard, Twitter seems to have a choice. The site can apply its resources to reducing this suspicious activity on its own terms or it can assume the governments that can make such demand are likely to crumble before any regulation can take place.
Categories